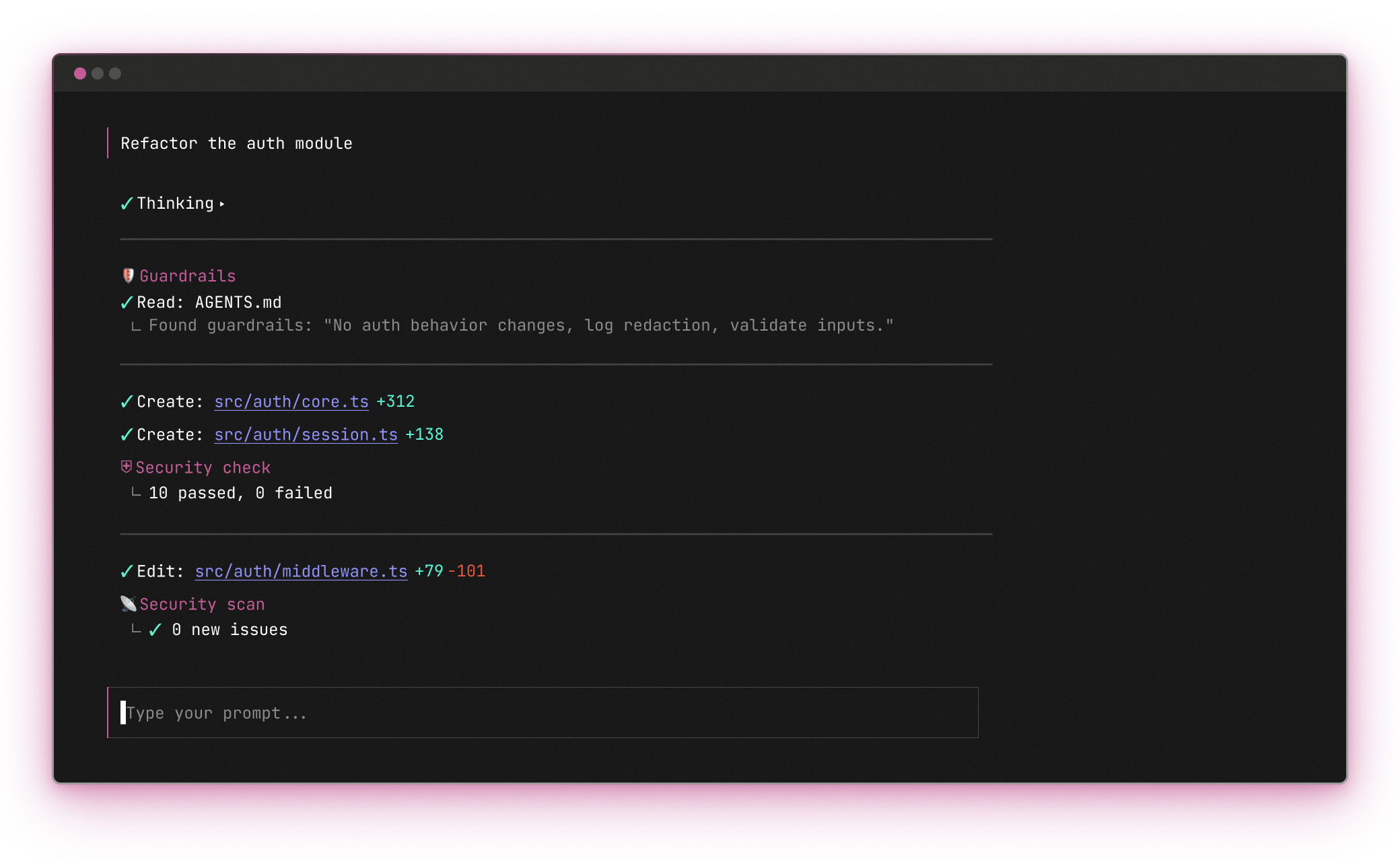
AI coding agents ship features fast, but most benchmarks never check whether the code is secure. In a controlled study of 100 projects, both Symbiotic Code and Claude Code ran on the same model (Claude Sonnet 4.6) against 50 neutral prompts across 5 languages. A deterministic SAST scan found 45 active vulnerabilities in Claude Code's output and zero in Symbiotic Code's — a 100% reduction across every language. An independent LLM judge scored Symbiotic Code higher on all 16 security and code-quality metrics, with an overall security score of 8.62 vs 5.58 (+3.04). The model is identical; the difference is Symbiotic Code's security harness — threat modeling before planning, org guardrails during implementation, and a deterministic scanner plus OWASP Top 10 audit afterward.